我们找出了如何使用最强大的免费软件实用程序之一来审核Linux系统。您是否想过Linux系统的安全性?有许多Linux发行版(每个发行版都有其自己的默认设置),在其中可以运行数十个具有不同版本号的软件包。另外,在后台的OS上,您有时不知道或想不到的许多服务。要获取有关系统的信息,即检查安装了Linux的计算机上运行的软件,网络和服务的一般状态,只需运行一些命令即可。但是现在如何处理收到的信息?怎么理解呢?毕竟,您需要分析的数据量巨大。如果您只运行一个可以生成有关系统安全级别的结构化报告的工具,那就更好了。Lynis是一种流行的开源工具,用于审核基于Linux和Unix的系统。“它对安全设置进行全面扫描,并在系统本身上运行。主要目标是测试安全功能并发布建议,以进一步提高系统安全级别。它还会扫描系统范围的信息,有关已安装软件包的信息以及可能的配置错误。该项目的网站说:“通常,系统管理员和安全专家会使用Lynis来评估系统安全级别。”安装Lynis
您可以使用程序包管理器来安装Lynis。如果您的Linux系统与存储库中版本的相关性正确,则可以按以下方式安装实用程序:dnf install lynis
或者:apt install lynis
但是,如果存储库中的实用程序版本不是最新的,则最好在GitHub上安装Lynis(我使用Red Hat Linux系统,但是类似的命令可在任何Linux发行版上运行):$ cat /etc/redhat-release
Red Hat Enterprise Linux Server release 7.8 (Maipo)
$
$ uname -r
3.10.0-1127.el7.x86_64
$
$ git clone https://github.com/CISOfy/lynis.git
Cloning into 'lynis'...
remote: Enumerating objects: 30, done.
remote: Counting objects: 100% (30/30), done.
remote: Compressing objects: 100% (30/30), done.
remote: Total 12566 (delta 15), reused 8 (delta 0), pack-reused 12536
Receiving objects: 100% (12566/12566), 6.36 MiB | 911.00 KiB/s, done.
Resolving deltas: 100% (9264/9264), done.
$
克隆存储库后,立即进入存储库,查看可用的存储库,然后找到一个名为lynis的文件。这实际上是一个shell脚本,因此您可以打开它并阅读它的作用。实际上,Lynis主要是使用脚本实现的:$ cd lynis/
$ ls
CHANGELOG.md CONTRIBUTING.md db developer.prf FAQ include LICENSE lynis.8 README SECURITY.md
CODE_OF_CONDUCT.md CONTRIBUTORS.md default.prf extras HAPPY_USERS.md INSTALL lynis plugins README.md
$
$ file lynis
lynis: POSIX shell script, ASCII text executable, with very long lines
$
启动Lynis
让我们通过使用-h标志运行帮助来开始使用Lynis :$ ./lynis -h
因此,您可以熟悉主要的实用程序命令。例如,让我们找出它的版本:$ ./lynis show version
3.0.0
$
有关Lynis命令的完整列表,请键入:$ ./lynis show commands
Commands:
lynis audit
lynis configure
lynis generate
lynis show
lynis update
lynis upload-only
$
对Linux系统进行审核
一切都从以下命令开始:$ ./lynis audit system
启动团队后,我们将收到详细的报告。不要惊慌,我们稍后会解决。其他团队工作结果也会保存,因此您以后可以返回。Lynis在这里存储日志: Files:
- Test and debug information : /var/log/lynis.log
- Report data : /var/log/lynis-report.dat
您可以检查是否实际创建了所有必需的文件:$ ls -l /var/log/lynis.log
-rw-r-----. 1 root root 341489 Apr 30 05:52 /var/log/lynis.log
$
$ ls -l /var/log/lynis-report.dat
-rw-r-----. 1 root root 638 Apr 30 05:55 /var/log/lynis-report.dat
$
我们研究报告
Lynis提供了相当详细的报告,因此我仅涵盖一些重要主题。Lynis在初始化期间要做的第一件事就是找出有关计算机上运行的操作系统的完整信息。然后,该实用程序会检查您已安装了哪些系统工具和插件:[+] Initializing program
------------------------------------
- Detecting OS... [ DONE ]
- Checking profiles... [ DONE ]
---------------------------------------------------
Program version: 3.0.0
Operating system: Linux
Operating system name: Red Hat Enterprise Linux Server 7.8 (Maipo)
Operating system version: 7.8
Kernel version: 3.10.0
Hardware platform: x86_64
Hostname: example
---------------------------------------------------
<<snip>>
[+] System Tools
------------------------------------
- Scanning available tools...
- Checking system binaries...
[+] Plugins (phase 1)
------------------------------------
Note: plugins have more extensive tests and may take several minutes to complete
- Plugin: pam
[..]
- Plugin: systemd
[................]
该报告分为不同的部分,每个部分均以[+]开头。一些部分可以在下面看到。[+] Boot and services
[+] Kernel
[+] Memory and Processes
[+] Users, Groups and Authentication
[+] Shells
[+] File systems
[+] USB Devices
[+] Storage
[+] NFS
[+] Name services
[+] Ports and packages
[+] Networking
[+] Printers and Spools
[+] Software: e-mail and messaging
[+] Software: firewalls
[+] Software: webserver
[+] SSH Support
[+] SNMP Support
[+] Databases
[+] LDAP Services
[+] PHP
[+] Squid Support
[+] Logging and files
[+] Insecure services
[+] Banners and identification
[+] Scheduled tasks
[+] Accounting
[+] Time and Synchronization
[+] Cryptography
[+] Virtualization
[+] Containers
[+] Security frameworks
[+] Software: file integrity
[+] Software: System tooling
[+] Software: Malware
[+] File Permissions
[+] Home directories
[+] Kernel Hardening
[+] Hardening
[+] Custom tests
为了更加清晰,Lynis使用颜色约定:- 绿色:一切都很好
- 黄色:没有找到所有必要的东西,或者出现了有争议的情况
- 红色:这是一个问题,值得处理
就我而言,大多数问题(红色标记)都在“内核强化”部分中找到。内核具有决定其操作的各种可配置参数,其中一些参数负责安全性。默认情况下,发行版可能由于各种原因未安装它们,但是您应该检查它们中的每一个,并查看是否需要根据安全性要求更改其值:[+] Kernel Hardening
------------------------------------
- Comparing sysctl key pairs with scan profile
- fs.protected_hardlinks (exp: 1) [ OK ]
- fs.protected_symlinks (exp: 1) [ OK ]
- fs.suid_dumpable (exp: 0) [ OK ]
- kernel.core_uses_pid (exp: 1) [ OK ]
- kernel.ctrl-alt-del (exp: 0) [ OK ]
- kernel.dmesg_restrict (exp: 1) [ DIFFERENT ]
- kernel.kptr_restrict (exp: 2) [ DIFFERENT ]
- kernel.randomize_va_space (exp: 2) [ OK ]
- kernel.sysrq (exp: 0) [ DIFFERENT ]
- kernel.yama.ptrace_scope (exp: 1 2 3) [ DIFFERENT ]
- net.ipv4.conf.all.accept_redirects (exp: 0) [ DIFFERENT ]
- net.ipv4.conf.all.accept_source_route (exp: 0) [ OK ]
- net.ipv4.conf.all.bootp_relay (exp: 0) [ OK ]
- net.ipv4.conf.all.forwarding (exp: 0) [ OK ]
- net.ipv4.conf.all.log_martians (exp: 1) [ DIFFERENT ]
- net.ipv4.conf.all.mc_forwarding (exp: 0) [ OK ]
- net.ipv4.conf.all.proxy_arp (exp: 0) [ OK ]
- net.ipv4.conf.all.rp_filter (exp: 1) [ OK ]
- net.ipv4.conf.all.send_redirects (exp: 0) [ DIFFERENT ]
- net.ipv4.conf.default.accept_redirects (exp: 0) [ DIFFERENT ]
- net.ipv4.conf.default.accept_source_route (exp: 0) [ OK ]
- net.ipv4.conf.default.log_martians (exp: 1) [ DIFFERENT ]
- net.ipv4.icmp_echo_ignore_broadcasts (exp: 1) [ OK ]
- net.ipv4.icmp_ignore_bogus_error_responses (exp: 1) [ OK ]
- net.ipv4.tcp_syncookies (exp: 1) [ OK ]
- net.ipv4.tcp_timestamps (exp: 0 1) [ OK ]
- net.ipv6.conf.all.accept_redirects (exp: 0) [ DIFFERENT ]
- net.ipv6.conf.all.accept_source_route (exp: 0) [ OK ]
- net.ipv6.conf.default.accept_redirects (exp: 0) [ DIFFERENT ]
- net.ipv6.conf.default.accept_source_route (exp: 0) [ OK ]
以SSH为例。这是系统的重要组成部分,必须加以保护。这里没有用红色突出显示任何内容,但是Lynis对于提高SSH服务的安全性有很多建议:[+] SSH Support
------------------------------------
- Checking running SSH daemon [ FOUND ]
- Searching SSH configuration [ FOUND ]
- OpenSSH option: AllowTcpForwarding [ SUGGESTION ]
- OpenSSH option: ClientAliveCountMax [ SUGGESTION ]
- OpenSSH option: ClientAliveInterval [ OK ]
- OpenSSH option: Compression [ SUGGESTION ]
- OpenSSH option: FingerprintHash [ OK ]
- OpenSSH option: GatewayPorts [ OK ]
- OpenSSH option: IgnoreRhosts [ OK ]
- OpenSSH option: LoginGraceTime [ OK ]
- OpenSSH option: LogLevel [ SUGGESTION ]
- OpenSSH option: MaxAuthTries [ SUGGESTION ]
- OpenSSH option: MaxSessions [ SUGGESTION ]
- OpenSSH option: PermitRootLogin [ SUGGESTION ]
- OpenSSH option: PermitUserEnvironment [ OK ]
- OpenSSH option: PermitTunnel [ OK ]
- OpenSSH option: Port [ SUGGESTION ]
- OpenSSH option: PrintLastLog [ OK ]
- OpenSSH option: StrictModes [ OK ]
- OpenSSH option: TCPKeepAlive [ SUGGESTION ]
- OpenSSH option: UseDNS [ SUGGESTION ]
- OpenSSH option: X11Forwarding [ SUGGESTION ]
- OpenSSH option: AllowAgentForwarding [ SUGGESTION ]
- OpenSSH option: UsePrivilegeSeparation [ OK ]
- OpenSSH option: AllowUsers [ NOT FOUND ]
- OpenSSH option: AllowGroups [ NOT FOUND ]
我的系统上没有运行任何容器或虚拟机。因此,可惜这里没有任何内容可供阅读。[+] Virtualization
------------------------------------
[+] Containers
------------------------------------
Lynis检查某些文件的特权,因为从安全角度来看,这很重要。[+] File Permissions
------------------------------------
- Starting file permissions check
File: /boot/grub2/grub.cfg [ SUGGESTION ]
File: /etc/cron.deny [ OK ]
File: /etc/crontab [ SUGGESTION ]
File: /etc/group [ OK ]
File: /etc/group- [ OK ]
File: /etc/hosts.allow [ OK ]
File: /etc/hosts.deny [ OK ]
File: /etc/issue [ OK ]
File: /etc/issue.net [ OK ]
File: /etc/motd [ OK ]
File: /etc/passwd [ OK ]
File: /etc/passwd- [ OK ]
File: /etc/ssh/sshd_config [ OK ]
Directory: /root/.ssh [ SUGGESTION ]
Directory: /etc/cron.d [ SUGGESTION ]
Directory: /etc/cron.daily [ SUGGESTION ]
Directory: /etc/cron.hourly [ SUGGESTION ]
Directory: /etc/cron.weekly [ SUGGESTION ]
Directory: /etc/cron.monthly [ SUGGESTION ]
在报告的结尾,Lynis根据审核结果进行更正。每个句子都以描述开头,并在其旁边的括号中指示生成该句子的测试(TEST-ID)。如果存在问题,则下一行提出解决方案:Suggestions (47):
----------------------------
* If not required, consider explicit disabling of core dump in /etc/security/limits.conf file [KRNL-5820]
https://cisofy.com/lynis/controls/KRNL-5820/
* Check PAM configuration, add rounds if applicable and expire passwords to encrypt with new values [AUTH-9229]
https://cisofy.com/lynis/controls/AUTH-9229/
Lynis可以使用show details命令,然后是TEST-ID测试编号,找到有关每个更正建议的其他信息:./lynis show details TEST-ID
例如,要查找有关SSH-7408测试的更多信息,请输入$ ./lynis显示详细信息SSH-7408并得到:$ ./lynis show details SSH-7408
2020-04-30 05:52:23 Performing test ID SSH-7408 (Check SSH specific defined options)
2020-04-30 05:52:23 Test: Checking specific defined options in /tmp/lynis.k8JwazmKc6
2020-04-30 05:52:23 Result: added additional options for OpenSSH < 7.5
2020-04-30 05:52:23 Test: Checking AllowTcpForwarding in /tmp/lynis.k8JwazmKc6
2020-04-30 05:52:23 Result: Option AllowTcpForwarding found
2020-04-30 05:52:23 Result: Option AllowTcpForwarding value is YES
2020-04-30 05:52:23 Result: OpenSSH option AllowTcpForwarding is in a weak configuration state and should be fixed
2020-04-30 05:52:23 Suggestion: Consider hardening SSH configuration [test:SSH-7408] [details:AllowTcpForwarding (set YES to NO)] [solution:-]
尽量不要折磨
因此,如果您想进一步了解Linux系统的安全性,请查看Lynis。而且,如果您想了解更多有关该实用程序如何工作,如何收集所有这些信息的信息,请深入其shell脚本。与其他实用程序一样,首先在虚拟机上进行尝试是有意义的。您使用什么工具?分享评论。
作为广告
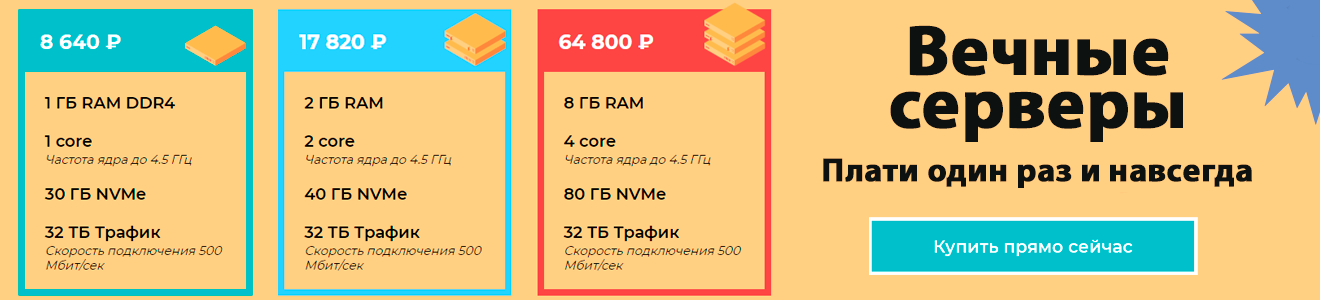
VDSina可在任何操作系统上提供服务器-选择预安装的操作系统之一,或从映像中安装。每日付款服务器或市场上独特的报价-永恒的服务器!