If you have repeatedly encountered large access lists or object-groups included in them, then you probably already wondered if there is a tool that allows you to determine whether an access list will skip a specific package and which lines will work.
Of course, such tools exist and completely or partially solve the listed problems. However, they, as a rule, are part of powerful "harvesters" of network management, 90% of the functionality of which you are not interested in.
Of course, no one forbids using regular expressions to search for specific access list lines directly from the console of a network device. But this method will provide a very superficial result. For example, it will not display the access of a host falling into a netmask or a port falling into a range. Moreover, in this way it is not possible to display all existing accesses between two given nodes or networks. An experienced network administrator is aware of the futility of the simple parsing access list for such tasks.
The considered small utility was created just for this - to find access-list lines that allow or prohibit certain network traffic, and even more - to identify all lines related to access between between given points.
The idea is simple: the program finds access list lines that match the specified criteria. The criterion itself looks like an access list string, but without using the permit or deny operator.
If you regularly add network rules to the access list without checking their existence, then access lists will contain a large number of redundant rules. To solve this problem, the program implements a redundancy access list analysis functional. With it, you can identify unnecessary rules and free up equipment resources.
When using object groups in ACLs, the program needs to transfer (copy) their composition. In the final ACL, such groups will be represented by elementary rules.
Program interface
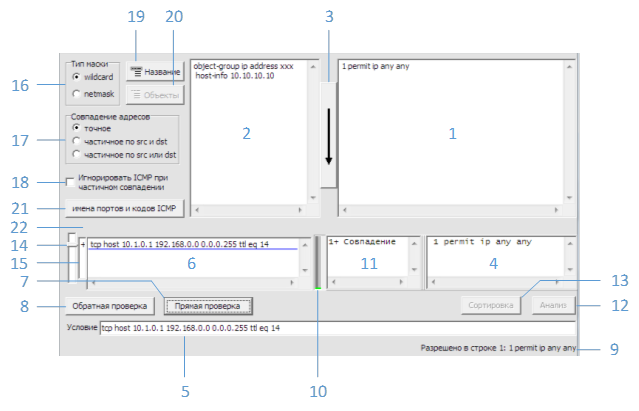
Fig. 1 Main window
Figure 1 shows the main program window with the following elements:
1 — access-
2 — object-
3 — access-
4 — access-
5 —
6 —
7 —
8 —
9 —
10 — ACL
11 — ACL
12 — ACL
13 — ACL
14 — (6)
15 — (6)
16 —
17 —
18 — ACL ICMP
19 — ACL CLI
20 — object-, ACL
21 — , ICMP
22 — ACL
access-list 1. object-, 2. ACL object- (“show running-config”, “show startup-config”), “show access-lists”, “show object”.
“show running-config”, 1:
ip access-list extended ACL
permit icmp host 172.16.0.6 host 172.21.0.6
permit ip host 172.16.0.6 host 172.21.0.1
permit tcp host 192.168.8.15 range 1024 65534 host 192.168.66.47
permit tcp 192.168.8.0 0.0.0.255 eq 22 1521 3389 addrgroup ADMIN_BSD
permit tcp host 192.168.8.12 eq 1521 192.168.83.20 0.0.0.1
access-list “show access-lists”:
Extended IP access list ACL
10 permit icmp host 172.16.0.6 host 172.21.0.6
20 permit ip host 172.16.0.6 host 172.21.0.1 (32 matches)
30 permit tcp host 192.168.8.15 range 1024 65534 host 192.168.66.47
40 permit tcp 192.168.8.0 0.0.0.255 eq 22 1521 3389 addrgroup ADMIN_BSD (1 match)
50 permit tcp host 192.168.8.12 eq 1521 192.168.83.20 0.0.0.1
“show running-config”, 2:
object-group ip address ADMIN_BSD
host-info 10.237.92.131
host-info 10.22.145.132
host-info 10.22.145.136
host-info 10.22.145.141
“show object-group”:
IP address object group ADMIN_BSD
host 10.237.92.131
host 10.22.145.132
host 10.22.145.136
host 10.22.145.141
object-.
“show running-config”:
object-group network Servers
host 10.15.12.5
host 10.15.5.11
host 10.15.4.2
host 10.15.7.34
object-group service Ports1
tcp-udp eq domain
tcp-udp eq 88
udp range 3268 3269
tcp gt 49151
“show object-group”:
Network object group Servers
host 10.15.12.5
host 10.15.5.11
host 10.15.4.2
host 10.15.7.34
Service object group Ports1
tcp-udp eq domain
tcp-udp eq 88
udp range 3268 3269
tcp gt 49151
:
object-group network zzz
5.5.5.0 255.255.255.0
host 6.6.6.6
object-group network yyy
host 3.3.3.3
group-object zzz
object-group network xxx
host 1.1.1.1
group-object zzz
group-object yyy
permit udp any object-group xxx eq 21
permit tcp object-group xxx host 7.7.7.7 eq ftp
permit tcp object-group xxx object-group xxx eq 22
permit tcp object-group yyy object-group xxx eq ftp
ACL object- 3. access-list ( object-) 4. , 22. .
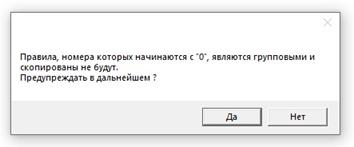
, object-, ‘0’ (.2).
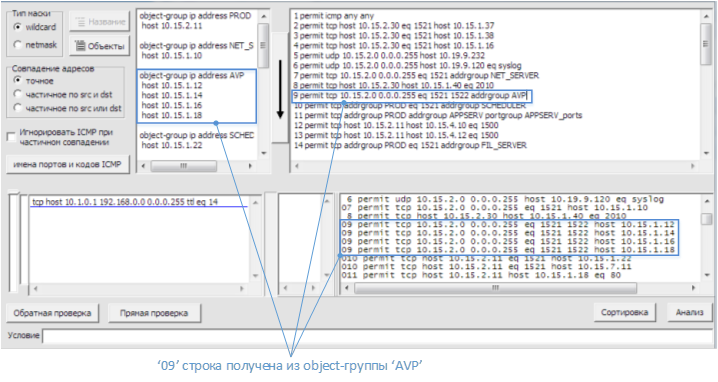
.2 object-
access- , 19, , access-. access- object- 20 (.3).
.3 object-
access- . .
, access- , 5 7. 9. 11. access- 10. “ ” 11 ACL, .
1. .
, 192.168.1.2 TCP 1521 192.168.2.2 :
ip access-list extended ACL
10 permit tcp 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255 range 1521 1522
20 permit tcp host 192.168.1.2 any
30 permit tcp host 192.168.1.3 any eq 1521
access- 1 3. 5 :
tcp host 192.168.1.2 gt 1023 host 192.168.2.2 eq 1521
7 “Enter”.
9 :
1: 10 permit tcp 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255 range 1521 1522
“1:” ACL, “10” – ACL. “ ” , ACL , . 11. ( ) “ ”, ACL.
2. , .
, , 192.168.2.0 /24 SSH (TCP 22). :
ip access-list extended ACL
10 permit tcp 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255 range 1521 1522
20 permit tcp any 192.168.2.0 0.0.0.3 eq 22 3389
30 permit tcp host 192.168.1.3 host 192.168.2.254
40 permit tcp host 192.168.1.10 any
access- 1 3.
17 “ src dst”. ACL, IP- , .
5 :
tcp any gt 1023 any eq 22
7 “Enter”.
9 :
11. ( ) “ ”, ACL. “?” .
3. , .
, 192.168.1.10 192.168.2.254 ACL:
ip access-list extended ACL
10 permit tcp 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255 range 1521 1522
20 permit tcp any 192.168.2.0 0.0.0.3 eq 22 3389
30 permit tcp host 192.168.1.3 host 192.168.2.254
40 permit tcp host 192.168.1.10 any
access- 1 3.
17 “ src dst”.
5 :
ip host 192.168.1.10 host 192.168.2.254
, access-, ACL . , ACL . (8), , “ ”.
8 “Ctrl-Enter”.
9 :
11. ( ) “ ”, ACL. “?” .
17 “ src dst”.
ICMP . IP ICMP. ICMP , ICMP access-. ICMP 18.
( 6)
(6) . , , . ( ) “Shift-Enter”. . 7 (Enter) 8 (Ctrl-Enter). 15 . . 14 .
( 13)
access-list, 4, . (13) (. . 4).
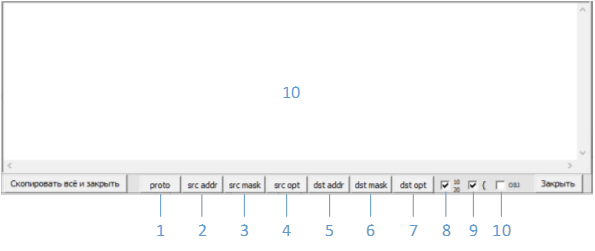
.4
1-7 —
8 —
9 —
10 — object-
.
:
1 permit udp 192.168.8.0 0.0.0.255 host 192.168.38.24 eq syslog
2 permit tcp 192.168.8.0 0.0.0.255 host 192.168.38.23 eq 1514
3 permit tcp 192.168.8.0 0.0.0.255 host 192.168.38.24 eq 1514
4 permit tcp 192.168.8.0 0.0.0.255 host 192.168.38.23 eq 4041
5 permit tcp 192.168.8.0 0.0.0.255 host 192.168.12.26
6 permit ip 192.168.8.0 0.0.0.255 192.168.41.0 0.0.0.255
7 permit ip 192.168.8.0 0.0.0.255 host 192.168.41.31
IP , , 5 1. 5.
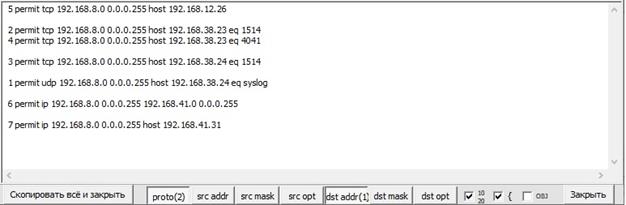
.5
. .
10 ACL object-. object- . . , object-, ACL. object- ACL , .
ACL:
10 permit tcp 192.168.8.0 0.0.0.255 eq 1521 addrgroup Empl_Center
20 permit udp 192.168.5.0 0.0.0.255 host 10.232.202.18
30 permit udp 192.168.8.0 0.0.0.255 host 192.168.7.34 eq ntp domain
40 permit tcp host 192.168.8.21 addrgroup HB_WEB_DMZ eq 12040 12060
50 permit tcp 192.168.8.0 0.0.0.255 eq 1521 host 10.237.49.254
object-:
object-group ip address Empl_Center
host-info 10.237.49.100
host-info 10.237.49.6
host-info 10.237.130.15
object-group ip address HB_WEB_DMZ
host-info 10.232.202.12
host-info 10.232.202.16
host-info 10.232.202.19
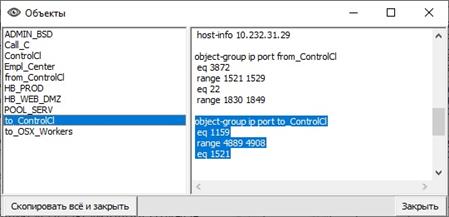
( “dst addr”) (.6):
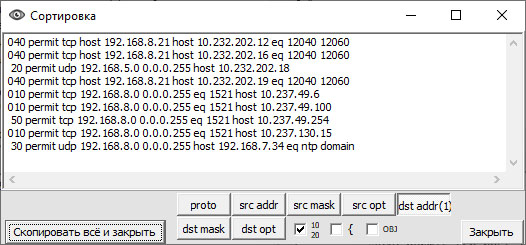
.6 object-.
“0” , object-. , 20 40.
object- ( 10). (.7):
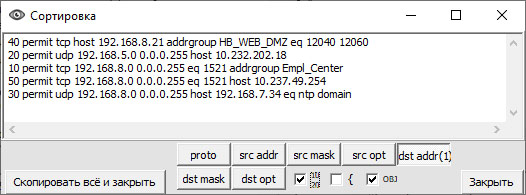
.7 object-.
ACL .
ACL, object-, , object-. ACL object- , .
( 12)
“” (12) access-. access- . access-, - (“deny” “permit” ).
, ACL:
10 permit icmp any any
20 permit tcp host 10.15.2.11 eq 1521 host 10.15.1.10
30 deny tcp 10.15.2.0 0.0.0.255 10.15.0.0 0.0.31.255
40 permit udp 10.15.2.0 0.0.0.255 host 10.19.9.232
50 permit udp 10.15.2.0 0.0.0.255 host 10.19.9.120 eq syslog
60 permit tcp host 10.15.2.11 eq 1521 host 10.15.7.11
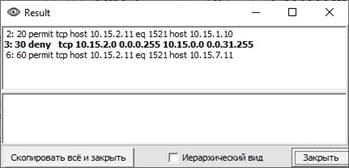
( 3) “” (12). (. 8):
.8
“” , (. 9):
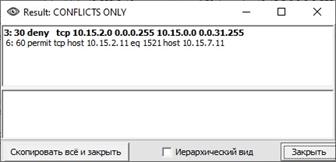
.9
‘’ (.8), , , .
access-list:
10 permit icmp any any
20 permit tcp host 192.168.1.10 host 192.168.2.20 eq 22
30 permit tcp host 192.168.1.10 host 192.168.2.20
40 permit ip 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255
ACL :
.10
, , ACL. . ( ) .
“Ctrl”, (.11):
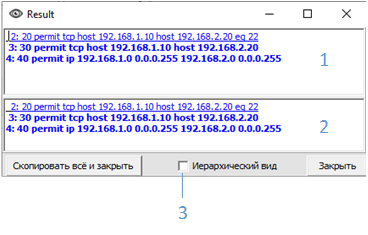
.11
1 —
2 —
3 —
2 3. , 3 4. (3). , . 1 ( ) :
- “C ”. 1 ;
- “ ‘no’”. ‘no’ . . ACL;
- “ ‘no’ ”. ‘no’ . ;
- “ ‘no’ , ”. , , . . ACL . ;
- “ ”. .
access-:
1 permit tcp any host 192.168.2.20 eq 22
2 permit tcp host 192.168.1.10 host 192.168.2.20 eq 22
3 permit tcp host 192.168.1.10 any eq 22
4 permit ip 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255
(.12) 2 :
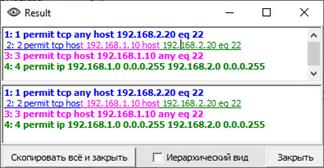
.12 .
().
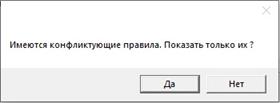
, access-, object-, , .. ACL . , (.13):
.13 .
“permit” “deny” ACL . ACL . , “deny”. , ACL ACL.
( 21)
21 TCP UDP, ICMP- (.14).
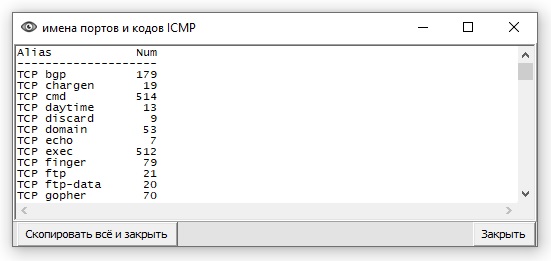
.14 ICMP.
exe-:
/ h, / ?, / help - call start parameters help
/ l (rus) - select language
/ nm - enable “netmask” mode
/ pm (and, or) - select address matching mode
/ skipicmp - enable “ignore ICMP when partial match. ”
Source Link